We don't just manage IT.
We own the outcome.
Fixed-price managed IT and security for businesses that want transparency, not excuses.
Sound familiar?
Most businesses put up with IT that does not work for them. These are the patterns we hear every week.
Your IT provider disappears when things break
You call, you wait, you chase. Reactive-only support means problems fester while you are stuck in a ticket queue. Your business keeps moving — your IT provider does not.
You have no idea what you're paying for
Opaque pricing, vague scope, and surprise invoices. You get a monthly bill but no clarity on what is included, what is extra, or whether you are getting value for money.
Security is an afterthought, bolted on after the breach
No proactive baseline, no hardening, no monitoring until something goes wrong. You find out your defences are weak only after they have already been breached.
A different kind of MSP
We built Tarbh Tech around three principles that address these problems head on.
Engineered Baseline
Every client environment is engineered towards a 75%+ Microsoft Secure Score target. We deploy a comprehensive security baseline before we consider the engagement live.
True Ownership
We do not just monitor. We manage. Your IT operations are our responsibility, governed by clear SLAs and published metrics. When something breaks, we fix it. When something needs improving, we recommend it and make it happen. Accountability is built into every engagement.
Fixed Per-User Pricing
No surprises. Published pricing, published scope. You see exactly what's included before you pick up the phone. Every tier includes our security baseline as standard.
Five tiers. One standard.
COSAINT (kuh-SAHNT) – from the Irish word for “protection”
Every tier includes our security baseline as standard. Pick the level of IT management that fits your business.
How we work
A three-stage operating model that builds security first, then keeps everything running and improving.
Baseline
We deploy our engineered security baseline across your environment. Every device, every identity, every mailbox — engineered towards a 75%+ Secure Score target.
Operate
We take full ownership of your IT operations. Helpdesk, monitoring, patching, user management — everything runs through our team. You focus on your business.
Improve
Monthly reporting, quarterly reviews, and continuous improvement. We identify opportunities, recommend changes, and keep your environment ahead of threats.
What every client gets
Our security baseline is included in every tier. These are the foundations we deploy before anything else.
Microsoft Secure Score optimisation
Every tenant engineered towards a 75%+ Secure Score target, adapted to your environment. Continuous monitoring detects drift.
Endpoint protection on every device
Microsoft Defender for Endpoint deployed and managed across all workstations, laptops, and mobile devices.
Email threat protection
Ironscales email security with AI-powered phishing detection, impersonation protection, and automated remediation.
Identity and access management
Entra ID with conditional access policies and multi-factor authentication. Zero-trust principles applied from day one.
CIS baseline alignment
Every tenant configured against CIS Microsoft 365 benchmarks. Documented controls that satisfy auditors and cyber insurance providers.
Monthly security reporting
Automated monthly reports covering Secure Score trends, incidents, threat landscape, and recommendations for improvement.
Live service dashboards
Real data from real clients. Updated automatically. Every metric published because transparency builds trust.
Real results, real businesses
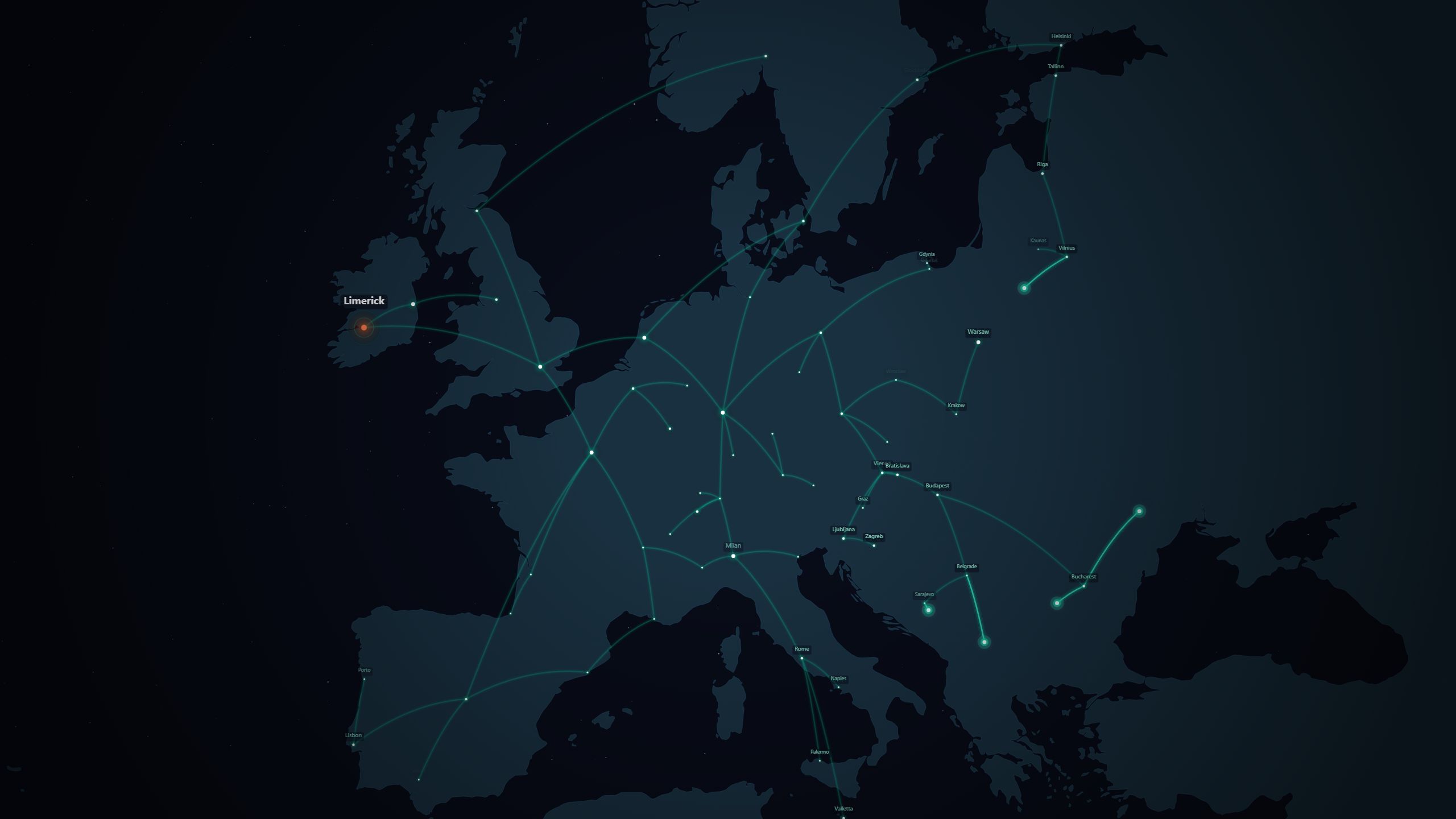
See how businesses across Europe transformed their IT security with Tarbh Tech.
Regulated manufacturer with flat, unsegmented network, consumer-grade hardware, and unknown third-party infrastructure. No network-level visibility or threat monitoring.
Fast-growing wholesale distributor with M365 licences but no security baseline, persistent printing problems, and manual invoice processing.
Pan-European retailer with 70+ accumulated Conditional Access policies, AiTM phishing attacks compromising accounts, and fragmented MFA enforcement across 12,000+ corporate users.
A fast-growing consultancy scaling across five countries needed a managed IT partner that could build a secure foundation across a macOS fleet, support multiple languages, and keep pace with headcount growth.
A growing IoT company with developers across four countries had no centralised device management, no security monitoring, and no way to evidence its posture to enterprise clients.
What People Say
What colleagues and clients say about working with us.
The work was of the highest standard. The team impressed from the very outset with their ideas, aptitude and diligent approach to tasks and projects. They also gave excellent contributions outside of their specific role and built up strong relationships with team members and other IT colleagues, with excellent contributions well beyond the brief.
Read full recommendation
The work was of the highest standard. The team impressed from the very outset with their ideas, aptitude and diligent approach to tasks and projects. In terms of automation engineering, they ticked all the boxes and more and met every requirement asked of them. They also gave excellent contributions outside of their specific role and built up strong relationships with team members and other IT colleagues in the relatively short time they were here, with excellent contributions well beyond the brief. If I could persuade them that the weather here is as nice as Sydney, I'd have them back on the team in a second.
– David M., Senior IT Leader, Asset Management
A consistent high performer. They needed little direction on the most complicated architecture designs and deployment activities. Always focussed on the task at hand and communicated well at all levels. Would work with again without hesitation.
Read full recommendation
I worked with the team for a few years and they were a consistent high performer. They needed little direction on the most complicated architecture designs and deployment activities. Always focussed on the task at hand and communicated well at all levels. Would work with again without hesitation.
– David H., SVP Enterprise Technology
A unique talent: the ability to operate at almost any level within large and complex IT environments. Extremely capable and regularly called upon to span teams and levels within teams to construct large scale infrastructures and resolve problems within and between them.
Read full recommendation
A unique talent: the ability to operate at almost any level within large and complex IT environments. Extremely capable and regularly called upon to span teams and levels within teams to construct large scale infrastructures and resolve problems within and between them. Also a very friendly, approachable team and ideal to work with. If I had the role to stretch those talents I would hire them tomorrow.
– Dermot R., Solutions Architect
The numbers speak for themselves
What a single in-house IT hire costs a ~50 user Irish business versus a managed service team.
In-House IT Hire
Single point of failure. Holiday cover, sick leave, and resignation risk not included.
Managed Service
50-user organisations rarely keep expert sysadmins engaged long-term. A managed service gives you a team of specialists for roughly half the cost of a single hire.
Industries we serve
We work with businesses across manufacturing, professional services, and technology sectors.
Get a Free Security Assessment
Understand your current security posture, identify gaps, and get actionable recommendations. No obligation, no sales pitch — just clarity.
Request Your AssessmentFrequently Asked Questions
What makes you different from other MSPs?
Do I need to be technical?
What if I'm locked into a contract with my current provider?
How quickly can you onboard us?
What size companies do you work with?
Is there a minimum commitment?
Does the per-user price cover everything?
Ready to talk?
No sales pressure. Just straight answers about your IT.
Or email us at [email protected]